5 White-Hat Hackers Working to Improve Cybersecurity
A computer geek might call himself a “hacker”, but to most people outside of the world of coding, that label carries pejorative overtones. The non-tech community generally assumes that hackers are involved in the illicit activities of breaking into government and corporate information systems either to steal data or simply to wreak havoc. Hackers, however, are not all bad.
A few more infamous hackers (most notably, Julian Assange, and Edward Snowden) occupy a gray zone between legitimate and illicit hacking and see themselves as freedom fighters who expose government wrongdoing. While their actions raise legitimate questions as to the validity of their motivations, other hackers are more clearly on the legitimate side of the equation. At least five individuals or groups of “white-hat” hackers are typically included on lists of legitimate code hackers.
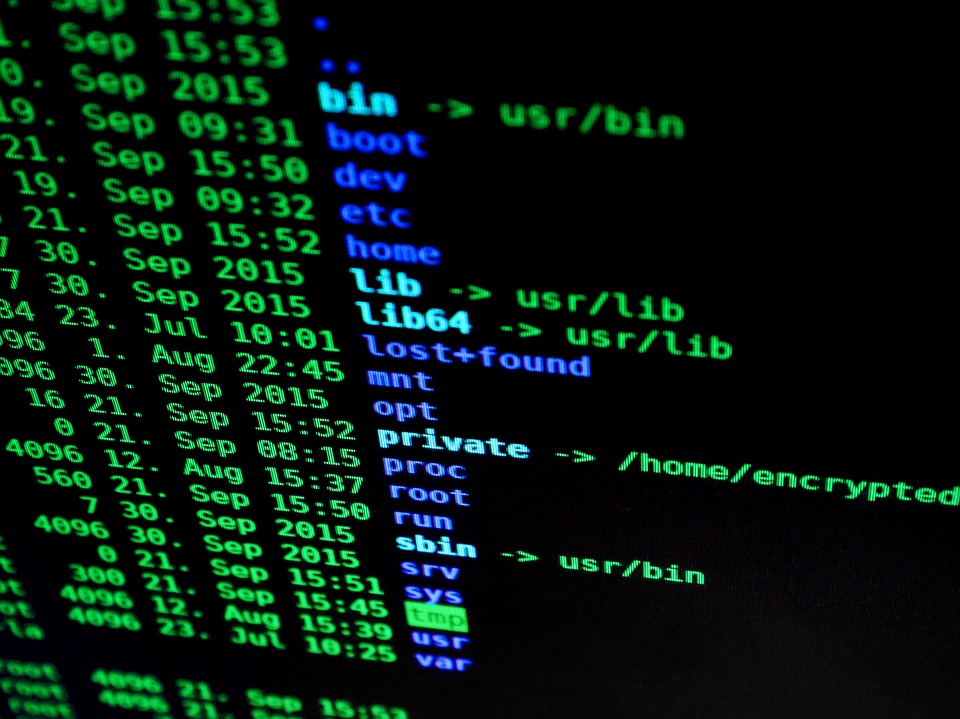
This entity was founded as a not-for-profit organization in 2012 by a group of cybersecurity researchers who saw an opportunity for collaboration among researchers who were trying to eliminate malware and other infectious code from the internet. The group maintains a malware analysis blog on which it lists the results of its research into malware that can infect networks that run on Linux. The group is credited with discovering and eliminating threats from numerous infectious pieces of software.
2. Kevin Mitnick and Mitnick Security
Kevin Mitnick styles himself as the world’s most famous hacker. Long before he formed his eponymous cybersecurity company, Mitnick hacked into the Los Angeles bus system and Digital Equipment Corporation’s computer network, as well as dozens of other corporate information systems. He served time in prison for his actions, and in the early 2000’s he turned his hacking skills into a legitimate business. One of his primary services is performing network penetration and phishing testing to detect weaknesses in an organization’s network.
3. EC Council
EC Council is a cybersecurity education entity that teaches coders how to hack and offers different degree programs and certifications to individuals who want to learn how to fight hacking fire with hacking counterfire. EC Council’s programs include classes on detecting and implementing countermeasures against distributed denial of service (DDoS) attacks, network penetrations, and mobile device security. One of EC Council’s more popular programs is an “Ethical Hacking” certification that teaches coders how to find computer network vulnerabilities using the same tools that a cyberthief might use.
4. Marc Maiffret/Beyond Trust Security
Maiffret cofounded eEYE Digital Security in 1998 as a vehicle for legitimate use of his hacking skills. He was one of the first hackers to find security flaws in Microsoft’s software products. His company merged with Beyond Trust, where he currently holds the title of Chief Technology Officer. He has testified before Congress on cybersecurity issues, including cybersecurity threats to private businesses and public infrastructure. He continues to be the public face of a white-hat hacking community that seeks to improve internet security.
5. Greg Hoglund
Hoglund distinguishes himself on this list as a prolific author and serial entrepreneur. He founded at least three cybersecurity companies and is the author of numerous books, articles, and conference presentations on cybersecurity issues. After a slew of corporate emails were leaked from one of his companies in 2011, he consulted with the FBI to track and uncover one of the world’s more notorious hacker groups.
Whatever their motivation, white-hat hackers continue to work on the right side of the law to enhance network security and to shut down other hackers who threaten that security. At least at present, no network security system is perfectly protected against unethical hacking. Cyber risk insurance is an important asset in every organization’s toolkit to recover assets that may be lost to unethical hackers. That insurance can compensate an affected organization for its direct losses from a successful hacking attack and for liabilities and fines that an organization might incur if it loses sensitive customer data.